There is information we know we’re sharing about ourselves; there is information being generated about us that we do not create; and information about us is generated—unbeknown to us—simply because of our connections to other people online. – Ganesh and Hankey in From Information Activism to the Politics of Data
In my quest to learn more about the politics of data, specifically around privacy, I turned to an expert in the field, Tactical Tech Collective (TTC), on whom I have a big, huge, crush. I want to be a part of this organization; I want all their knowledge in my head. I examined their 2016 Annual Report, which details their work and progress. Then to focus on the unintended privacy mistakes I and others make, I looked to the article, An Honest Picture of Metadata: Exposing the Invisible, by Michael Kreil. To remedy those mistakes, I turned to From Information Activism to the Politics of Data by Maya Indira Ganesh and Stephanie Hankey.
Tactical Tech is all about data, specifically about privacy, use, and advocacy, and what we can do as individuals to protect our data from both ourselves and others. They offer tool kits, guides, training, and events to aid people in becoming more deliberate and informed users. Since 2014, Tactical Tech’s work has been organized around three central themes:
- Exposing and Shaping Issues – Using internet-based data, digital technology and data visualization to “uncover and investigate corruption and abuse of power.”
- Defending Essential Freedoms – Building digital security awareness and skills of advocates and activists through focused training and network-building.
- Politics of Data – Investigating data as it relates to privacy and connectivity. Recommends tools and information for use by individual technology users to keep and maintain control over their personal data.
Much of TTC’s work revolves around the goal of protecting the privacy rights of activists. One of the roadblocks to achieving this goal is that while there are a wide range of opportunities for interaction and for furthering the causes of activism via the digital environment, many activists/people have developed bad online habits. To help protect activists, thus ensuring their work continues, TTC wants to provide simple solutions for switching from habitual choices to choices that “resist, challenge, or subvert” the status quo. Specifically, this means selecting and using alternative providers for software, storage, and communication. To minimize our digital traces, Tactical Tech recommends choosing non-commercial or open source alternatives for everything from email to social networking, employing “circumvention technologies and opting out of participatory practices associated with the sharing economy.” These actions alone can provide greater personal and data security.
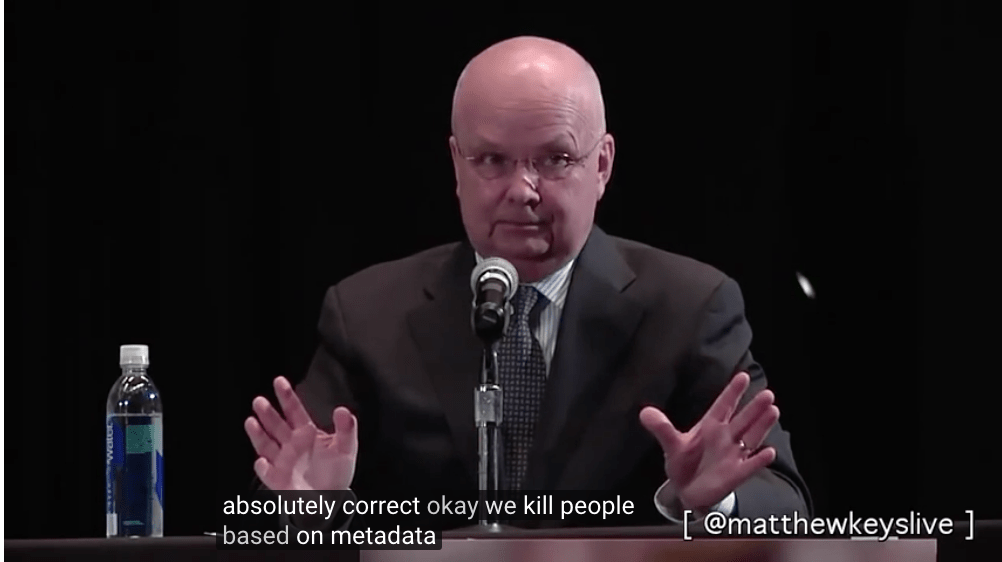
That being said, Ganesh and Hankey also noted that they are aware that the NSA and the GCHQ (the UK’s version of the NSA) are monitoring people who use circumventing browsers and other “privacy enhancing” strategies. The article then links to a video clip of a debate between General Michael Hayden, former director of the CIA and NSA, and Dr. David Cole, Georgetown professor of constitutional law, discussing the “balance between personal privacy and national security.” Hayden states that we need to draw the distinction between what could be done with our data, and what is being done with our data. Unfortunately, I can see how what is being done could change, depending on who is in charge at any given moment. Hayden is not exaggerating when he says, “We kill people based on Metadata.”
The data that leaves the “messiest, and least visible traces is metadata.” That is the data that is related to all the information we consume online, and the information that we create. Sometimes, our data intersects with others, without our actually clicking, or connecting to something, based on algorithms created by the program or software. Tactical Tech offers a website, myshadow.org that offers practical, easy to understand information and tools to combat this inadvertent attachment of ourselves and our data to others. We may not all be activists that need to protect ourselves from the government or other forms of surveillance, but that doesn’t mean that we can’t take steps to prevent our data from being used by corporations, with or without our permission, for their own gain. When larger numbers of people gain awareness of what their data is being used for, this may motivate them to participate in different habit, which lead to changes that can benefit all consumers.
When asked, “Have you got an alternative name for Metadata?” Michael Kreil responded, affirmatively with, “Data.” Kreil’s premise in An Honest Picture of Metadata is that the “extra” data, or metadata, that is attached to data (an email, a photo, etc.) is actually the data, because it can be analyzed to show patterns and it provides actual information, while something like text or photos are much more difficult to analyze and work with in bulk.
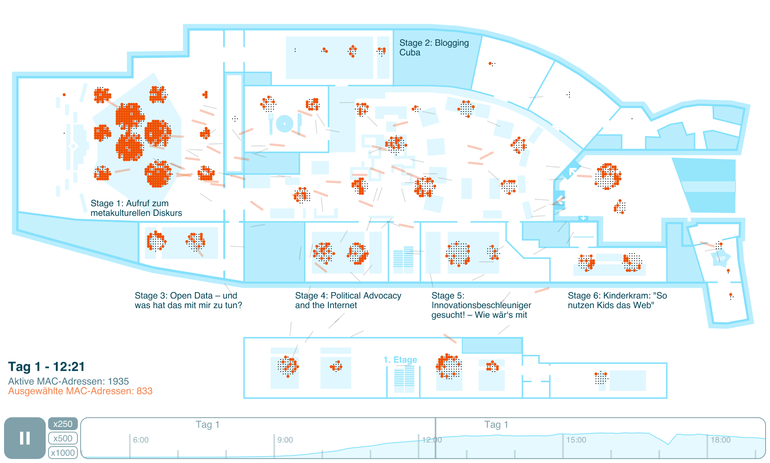
Kreil tested this out with his project, Re:log, based on anonymized location data he received from Re:publica conference goers who had hooked into, and used the conference’s Wi-Fi system. This data showed the different rooms and stages where people had logged-in, from which Kreil created a visualization of this usage with a floorplan of the conference venue and dots to indicate users. The most important thing for Kreil in publishing this project was to “make people think about surveillance.” While there are a lot of progressive, interesting, and harmless ways to connect people together using this data (similar interests, goals, work focus), there is also the chance that this information could be used to do harm (privacy invasion, stalking). Harm may not always be the intention, however it is important to be aware of the possibility, so users can take appropriate measures to protect themselves, depending on the level of comfort they have with the information being shared.
Kriel has done otherinteresting projects using data produced by the tracking of mobile devices and geolocation data on apps. In doing these projects he found that while it is becoming “increasingly difficult to control [our] data and information,” if we understand our data, we can take steps to control its flow and use.
These articles gave me pause. I know I am leaving data all over the place, but what I was not previously aware of was that my data was attaching to others, thus creating a picture of me, that may or may not be accurate. What helps to combat invasions of digital privacy is to understand how the data is being used – where connections are being made by users, to other users, and organizations, and what the results are of those connections. We have the ability to control how our data is used, but that means we need to be specific and deliberate about our own digital habits. I am now also very much aware that even though I have nothing to hide from the government, if I decide to protect my online privacy, and download and use Tor, because why not, I have now increased my chances of government surveillance. I literally just made myself 100% more suspicious than I was 30 seconds earlier. We must be able to answer the question, “Who uses my data, and for what purposes?”
Ganesh, M.I. and Hankey, S. (Aff1) (n.d.). FCJMESH-006 From Information Activism to the Politics of Data | The Fibreculture Journal : 26. Twentysix.fibreculturejournal.org. Retrieved from http://twentysix.fibreculturejournal.org/fcjmesh-006-from-information-activism-to-the-politics-of-data/#para19
John Hopkins University (April 7, 2014). The Johns Hopkins Foreign Affairs Symposium Presents: The Price of Privacy: Re-Evaluating the NSA – YouTube. Youtube.com. Retrieved from https://www.youtube.com/watch?v=kV2HDM86XgI
Kreil, M. (n.d.). Michael Kreil: An Honest Picture of Metadata | Exposing the Invisible. Exposingtheinvisible.org. Retrieved from http://exposingtheinvisible.org/resources/michael-kreil